Help IT automate workflows and resolve requests
GoSearch unifies your technical stack and automates routine support. Use AI-driven search, agents, and workflows to reduce ticket volume and maintain a secure, connected digital workspace.
IT teams power AI workflows with GoSearch
Empower your IT desk with AI that understands your environment and automates the manual tasks that slow down operations.
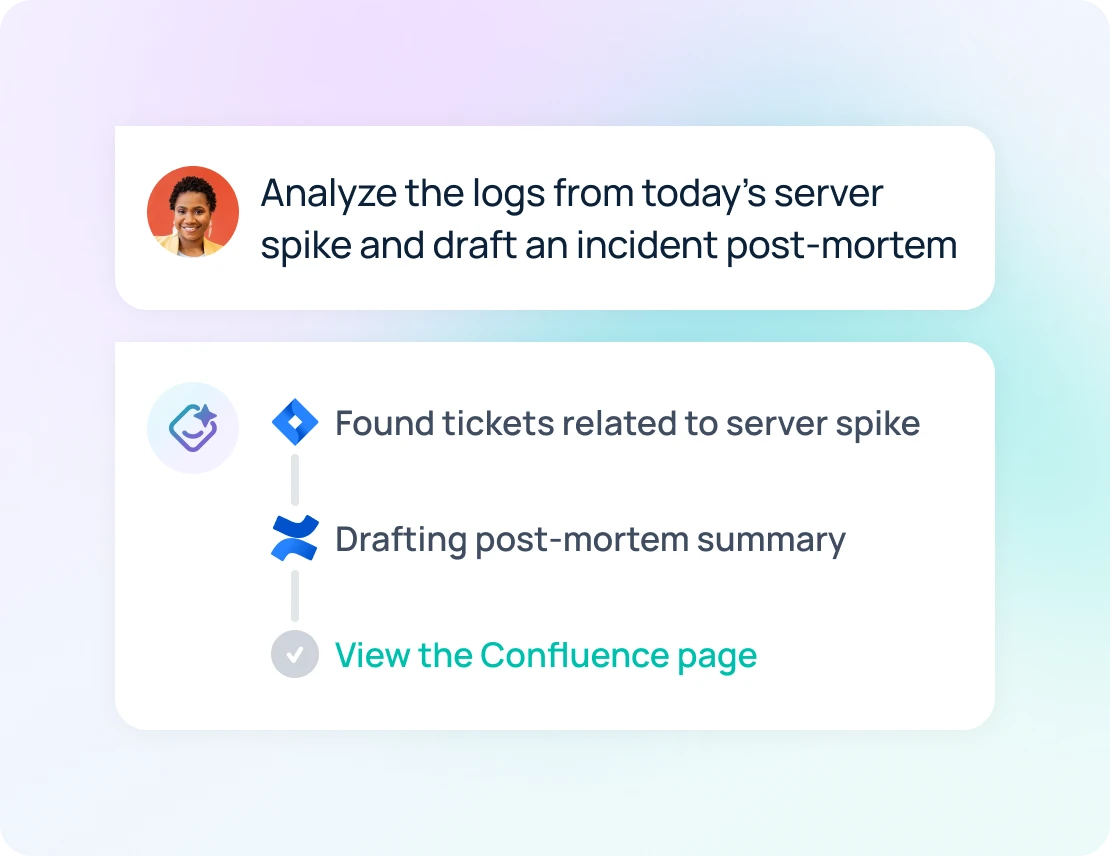
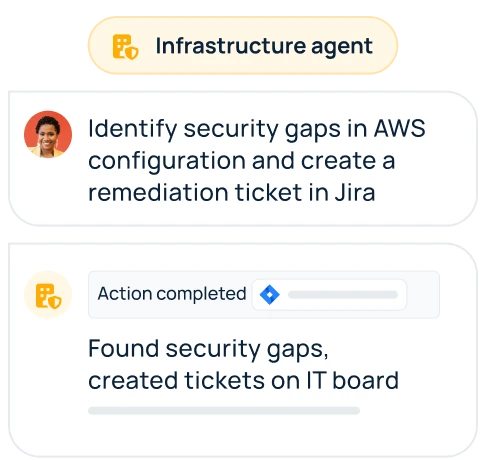
Tailored AI agents that scale IT support
GoSearch AI agents transform IT requests into resolutions. Agents handle repetitive support tasks, summarizing internal knowledge base articles and providing troubleshooting steps directly from your documentation. Offload routine inquiries so your team can focus on high-priority infrastructure.
Discover GoAI assistant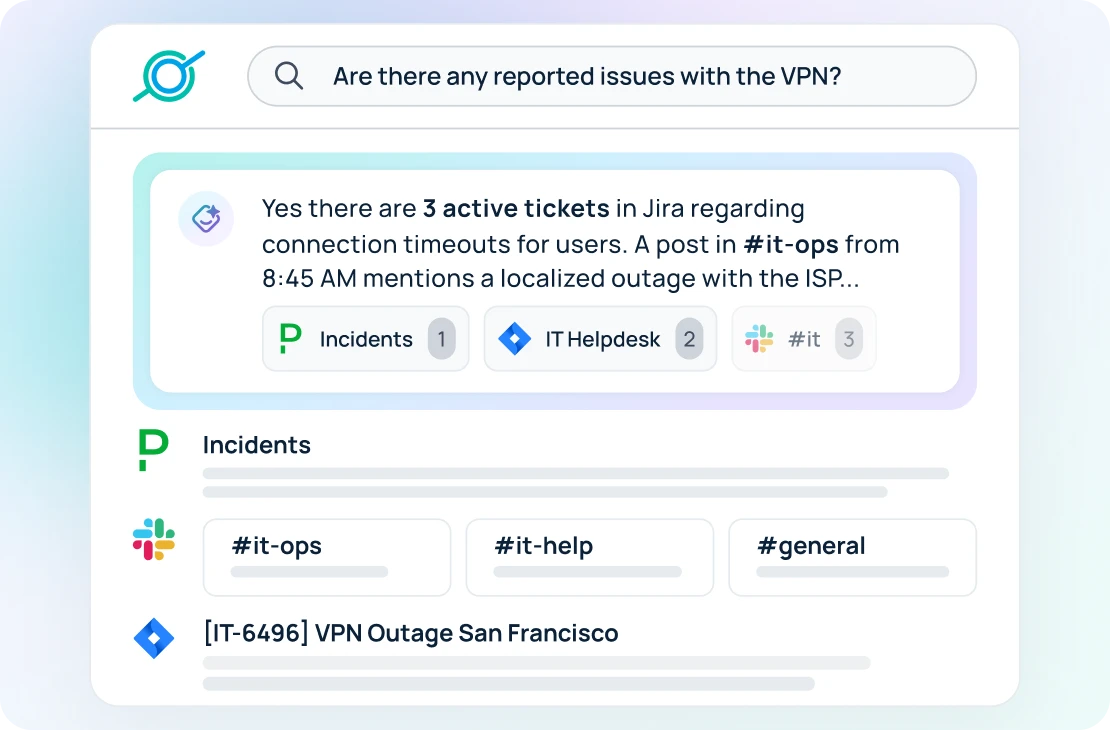
Instant visibility across your IT stack
Find exact configuration details, asset records, or security protocols in seconds. GoSearch connects your entire ecosystem to surface precise answers in real time. IT managers stay informed and resolve issues quickly without navigating between systems.
Learn about GoSearch enterprise search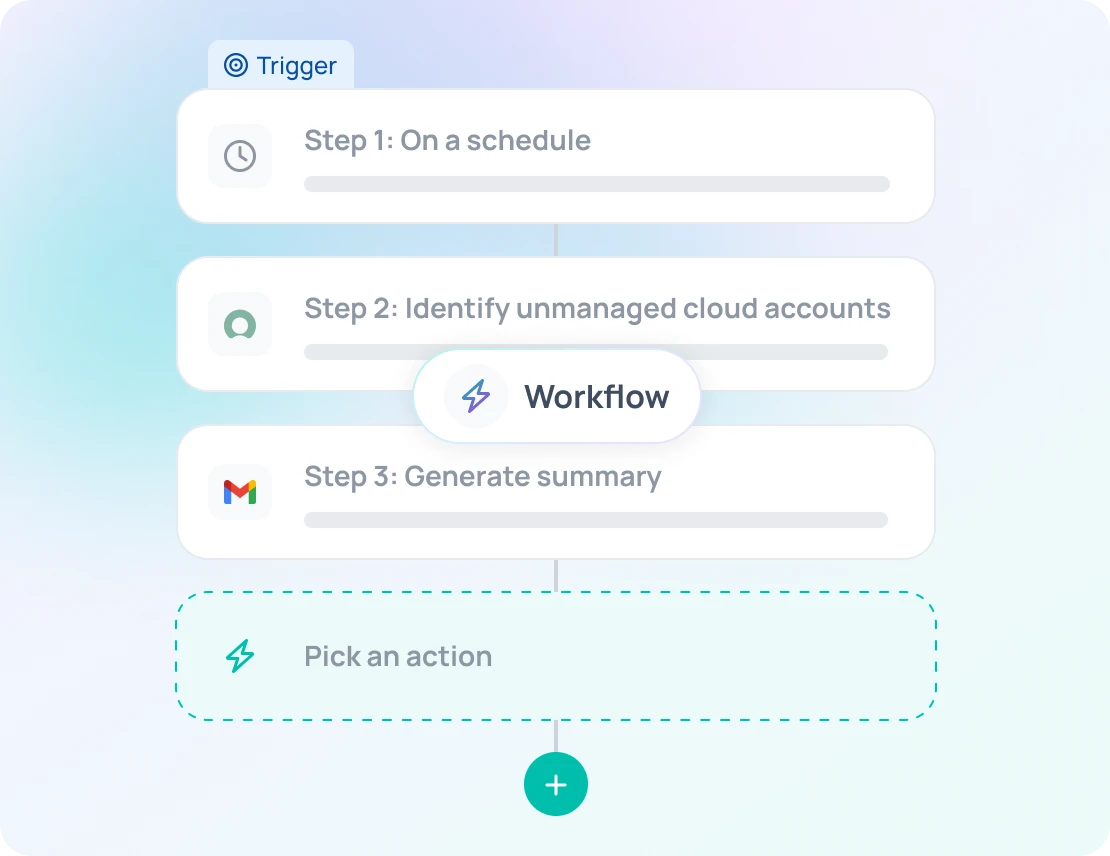
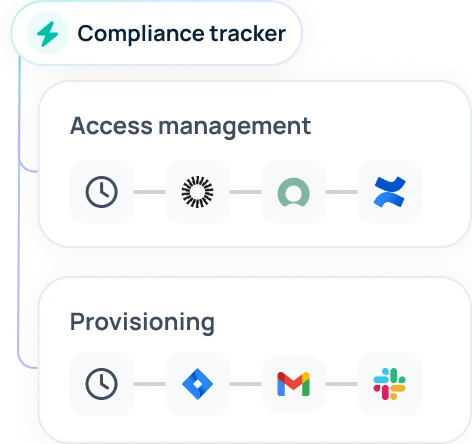
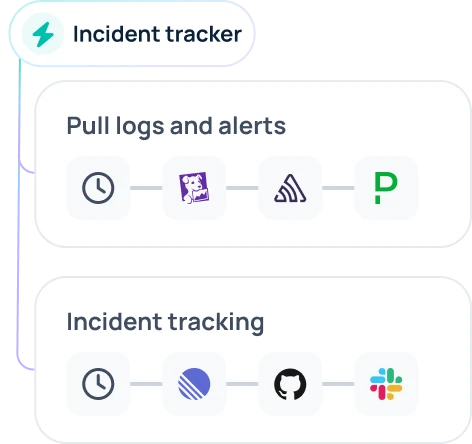
IT workflow automation, no coding required
Eliminate process bottlenecks and administrative friction across the service desk. Trigger actions across your IT tools, from hardware provisioning to software access requests, with a visual, no-code builder. Coordinate complex operations automatically while keeping your team aligned.
Explore GoSearch agents and workflowsYour enterprise tech stack in one view
Connect 100+ apps with hybrid data management — indexed, federated, or custom MCP retrieval.
See GoSearch integrationsBuild custom AI agents for IT automation
Design custom AI agents that understand your environment, handle repetitive tasks, and eliminate friction within your service desk.
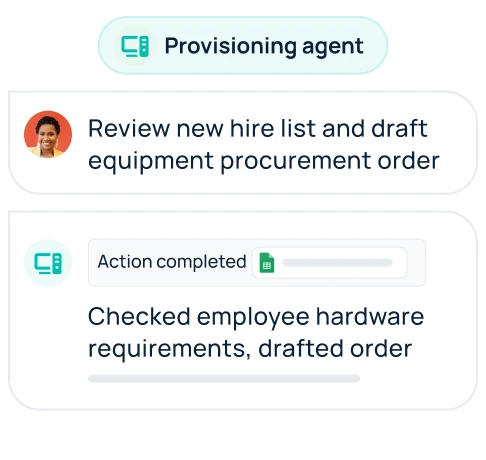
Equipment provisioning
Track inventory, manage hardware requests
Infrastructure monitoring
Detect outages, analyze system logs
Security compliance
Audit access logs, identify vulnerabilities
Incident reporting
Summarize error logs, track resolution steps
Enterprise-grade security and governance
Maintain full visibility and compliance while providing the speed and flexibility required for modern IT environments.
See GoSearch security
SOC 2 Type II certified
Rigorous third-party auditing of our security and operational controls.

Zero data retention
Your queries and data are never stored or used for model training.
BYO Cloud and BYO LLM
Full data sovereignty with deployment in your own VPC and models.
Explore more ways teams use GoSearch

















